阅读:0
听报道
The International Conference Computer Networks Histories: Local, National and Transnational Perspectives was held in Lugano, Switzerland on 14th -15th December 2017. The conference was organized by the association Geschichte und Informatik, the Institute of Media and Journalism & the China Media Observatory at the Università della Svizzera italiana and .
Network Spirits
-- Illustrated Conference Report by Vlad Atanasiu,University of Fribourg
本文摘取会议综述部分内容
01 EMBEDDING TOPOLOGIES
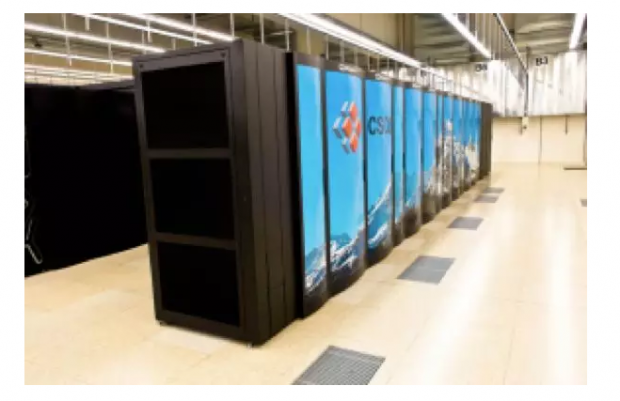
The picture above shows Europe’s fastest supercomputer in 2017, “Piz Daint” of the Swiss National Supercomputing Centre (CSCS), situated in the city of Lugano, on the southern slopes of the Alps. The rumbling emanating from the machine is not much different from that of an ancestral mill, only that it is not wheat or corn, but digital data that is crunched at the rate of 25 Petaflops. The data arrives and departs through 100 Gbit/s optic fiber cables set over the mountain passes of St Gothard, Simplon, and St Bernardino, serving academic institutions spread throughout the country, the CERN – cradle of the World Wide Web – at the French border, and various customers in the wider world.
The physical topology of the modern network thus closely follows that of 2000 years old Roman roads, themselves paved over neolithical trails. As for the excentric location of the supercomputing center, at five to seven train hours from the principal Swiss cities, such as Berne, Geneva, and Zurich, it is due to the battle of Marignano in year 1515. Having conducted during the 15th century crushing military campaigns against the German Empire to the North and the Burgundians in the West, the Swiss expansion into Italy was stopped by the King of France, François I, near Milan, about an hour drive from Lugano. In view of an equitable distribution of ressources between the four linguistic areas of modern Switzerland, a political decision was taken by the federal state in 1991 to allocate the newly to be established center for supercomputing to the Italian speaking canton of Ticino – that territory conquered 500 years ago.
The place is appropriate from a further point of view, namely that of the beautiful Lake Lugano. As it happens, the center consumes up to 11 Megawatts, in the future possibly even 25 MW, for suppling energy and cooling “Piz Daint” and the other, older, supercomputers. The necessary water is pumped from the nearby lake in 45 meters depth at the conveniently low temperature of 6 degrees Celsius and spilled back at 6 meters depth and no more than 25 degrees. On one hand digital Switzerland is hence taking advantage of the plate tectonics that eons ago created the Alps and the passing of the glacial era that dotted them blue with lakes, while on the other hand the circular water dynamics set in motion by the needs of supercomputing is sus- - 3 - pected, so the CSCS, to help rejuvenate the biotope of the heavily polluted Lugano lake.
Switzerland is a beautiful country and roundabout detours, through its picturesque countryside or intruiging history, should be refreshing and instructive. For example, for the purpose of introducing a seminal theme of the conference reviewed here: the realization of how much modern computer networks are tributary of preexisting topologies. From “longue durée” factors to events of the immediate present, from global trends to local particularities, physical networks and networked virtual worlds are embedded in a spatio-temporal scale-space topology; one that is also cultural, dominated by such dimensions as language, mentalities, and power. It might be useful to conceive these topologies as the spirits of the network, in reference to the Roman “genius locii” or the “sprites” of folktales and computer games, which albeit invisible factor into our lives. Let us listen to their signals.
The role of historians, journalists, and other inquisitors of the human mind and society, is to make the invisible visible, and in this respect the conference participants have succeeded in collectively creating a marvelous kaleidoscope of technological history. The following texts highlight a specific aspect of each presentation from the perspective of the reviewer, as a teaser for the forthcoming proceedings to be published in 2019 by the Swiss Association for History and Computing.
02 INTERNET METAPHORS

“Chinese! How far are you from the Information Highway? 1500 meters Northwards!” Thus prodded a Peking billboard in 1995 people towards one of the first public Internet access points in the country.
The Chinese word for information, xìnxī 信息, is a compound of two ideograms with the semantic fields of “letter”, “true”, “believe”, and “news”, “interest”, respectively. Thus Information Highway could be understood as positively connotated, a true path (Tao in Buddhism) towards enlightment (Zen). This is at least how the Californians saw things when the first APANET connections were established between the sunny beaches and the snowy Utah mountains. Alas, while the surfers might enjoy the scenery, where the road winds up is not in their hands. Governments throughout world history have been keen to control the strategical assets that are road and communication networks and convince the populations that the services they offer are not “fake news”. The Chinese writing system, much more than Indoeuropean etymology, makes the double sidedness of Internet metaphors almost physically present. That metaphors are shaping how we think – George Lakoff’s famous thesis – is self-evidence in Chinese politics. Let us move along this line with a couple more examples from Hu Yong’s conference presentation.
In Imperial China the government was located at the Heavenly Peace Gate, or Tienanmen, a proximity to the heavens facilitating its power to “make rain and fine weather” (as Conrad expressed unfettered power in Heart of Darkness), in other words to decide if the “Cloud” of computing is a fluffy, benevolent creature or a dark and menacing monster, which drowns you in the torrents of data with which you yourself feed its unstilled hunger of knowing everything about everybody.
The “Great China Firewall” is another great metaphor, in the spirit of Chairmen Mao’s slogan “Anything foreign is food to us.” The idea is that China has to adopt useful Western technology, but keep Westerners out and preserve its own mores. This attitude of the Middle Empire towards the peripheral world is deeply ingrained in its millennial history and made tangible through the Great Chinese Wall, supposed to defend against the Northern Barbarians – who despite it managed to rule the country, as Mongols (1271–1368), then Manchus (1644–1912). Westerners came from the sea, were there was no wall, a situation that should not be repeated in the case of the open frontier of cyberspace, hence the rush of the Chinese dragon to build a digital wall of fire around its dominion. The pyrotechnic filtering technology is of course Western export ware, but adapted to Chinese Communist ideals.
---
Hu Yong / Peking University / The metaphoric Chinese Cyberspace: The highway, the wall and the cloud
03 CYBER-SOVEREIGNTY

Words such as cyberspace, website, portal, and Geonames attest to how fundamentally online activity is conceived of in spatial terms. It is a small step therefore to translate concepts from the physical to the virtual world, such as “sovereignty”. Clément Renaud and Grégory Bahde reveal a consistent string of such analogies and their implications. Taking European history as an example, the Peace of Westphalia of 1648 – that put an end to thirty terrible years of religion wars – was an experimental laboratory for the modern concept of sovereignty and the practice of international diplomacy. We witness today a similar situation, in which states are probing the nature of cyberspace and how to deal with it in practical and legal terms. The reproduction in the virtual world of historical models is one method, exemplified by “cyber-pirates”, autonomous entities sometimes acting on behalf of sovereign states. The term “cyber-mercenary” has not gained widespread traction, but a “Declaration of Independence of Cyberspace” was already proclaimed in 1996 by the Electronic Frontier Foundation (another spatial metaphor), and while short of openly declared “cyber-wars”, state sponsored “cyber-attacks” have become the new normality.
---
Clément Renaud, Grégory Bahde / École Polytechnique de Lausanne, Université Jean Monnet St Etienne / From Davos to Beijing: The historical trajectory of the concept of sovereignty in Internet territories
04 DISOBEYING NETWORKS

The history of computer networks is often particular to a place, as it became apparent with each passing presentation in the conference; but one thing they seem to share: “Networks disobey their designers!”, said Benjamin Peters, veering between a legal finding and a revolutionary manifesto. As proof was offered a comparison of three case studies: the USSR, Chile, and the USA. The Soviets had a good head-start in the 1950 to build something like the “Internet archipelago”, with accomplishments such as the Sputnik satellite and Gagarin’s space travel, but due to bureaucratic and political squabbles, nothing came out of the supremacist sounding 1960s OGAS: the All-State Automated System for the Gathering and Processing of Information for the Accounting, Planning, and Governance of the National Economy, USSR. Meanwhile in Chile, the socialist government of President Alende arrived so far with designing as to have the Star Trekish control room of their version of cybernetic control of the society actually build. Once again, the future of the network was not to be what it was planned, General Pinochet and the CIA putting an abrupt and bloody end to the experiment. The only successful network was that of “capitalists acting as communists”: the American ARPANET was organizationally a rather topdown enterprise, resulting in a rather tree-like network. So much for state ideologies and actual behavior...
---
Benjamin Peters / University of Tulsa / The network and the historian: opportunities, challenges, surprises, disobedience
«computer-networks-histories-local-national-and-transnational
话题:
0
推荐
财新博客版权声明:财新博客所发布文章及图片之版权属博主本人及/或相关权利人所有,未经博主及/或相关权利人单独授权,任何网站、平面媒体不得予以转载。财新网对相关媒体的网站信息内容转载授权并不包括财新博客的文章及图片。博客文章均为作者个人观点,不代表财新网的立场和观点。



 京公网安备 11010502034662号
京公网安备 11010502034662号 